What seemed to be, or I hoped, was a trickle has given way to an ever increasing rise in the number of reported incidents on the compromise of government network resources. I’ll leave the “reported” clarifier to the clever and dedicated sleuths and investigative reporters.
Minus the powers of a crystal ball, I suppose we all agree attempts to access our information technology infrastructures will not soon abate. Hold onto your hats (and your data)…here are some recent occurrences and an analysis of the pertinent bid requests and RFPs.

It would be fair to expect that the federal government would have means in place to prevent or deter cyber attacks. The attacks are targeting the U.S. government. the guardian, Jun 5th, 2015, ‘OPB hack: China blamed for massive breach of US government data’. “The Obama administration is scrambling to assess the impact of a massive data breach involving the agency that handles security clearances and US government employee records…”
President Obama recently expressed that corrective action(s) are underway, “What we are doing is going agency by agency, and figuring out what can we fix with better practices and better computer hygiene by personnel.” The New York Times, Jun 5th, 2015, ‘U.S. Was Warned of System Open to Cyberattacks’. “A number of administration officials on Friday painted a picture of a government office struggling to catch up, with the Chinese ahead of them at every step.”
For certain, their guys aren’t smart enough to undermine our I.T. security. Stars and Stripes, Jun 8th, 2015, ‘Pro-Syrian government hackers force US Army website offline’. “The Syrian Electronic Army boasted of the hack on Twitter and shared an image of an anti-U.S. message posted before the website went completely dark.”
I’ve never worked for the federal government…while this is troubling, it doesn’t directly impact me. ABC News, Jun 7th, 2015, ‘Feds Looking Into Whether Attack of US Government Affected Private Citizens Too’. “In particular, investigators are considering the possibility that private citizens who never worked for the U.S. government may have also had personal information compromised, sources said.”
My curiosity and concern took me to ask the very simple question, “What are public sector agencies doing about it?” At a glance of the data, a lot.
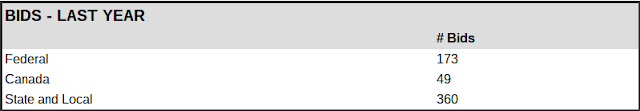
Along with their in-house cyber security measures, since January 1, 2015, U.S. government agencies have submitted 234 requests for cyber/network security solutions and services. An analysis going back the past year, there were a staggering 533 such requests published.
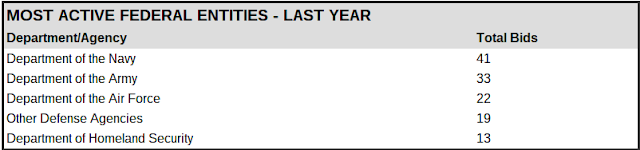
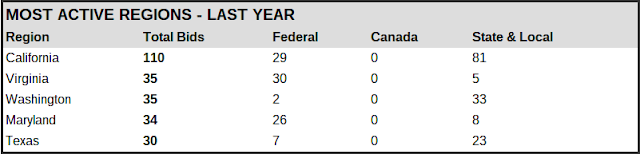
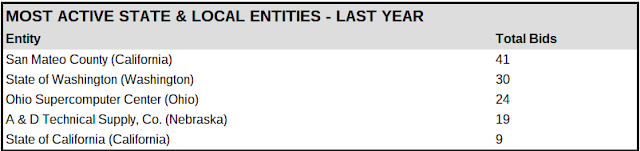
Here’s a breakdown of the government bid / RFP data covering the past 365 days.
In particular, the Department of Defense has been very active in procuring outside assistance.
Not surprising, the regions with a significant government presence are generating a large proportion of the activity.
The epicenter of the Silicon Valley, it’s easy to understand how San Mateo County is the most active SLED entity.
Sample Active Bids/RFPs
Cybersecurity
Due to the critical nature of the subject matter, we will soon undertake a continuing evaluation of developments pertaining to public sector cyber and network security. Any comments, questions, references for us to review, let us know.
For more information, visit BidPrime or call us at 888.808.5356.

